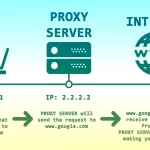
Whether you’re just starting or you’ve been using a proxy for a while, there are a few situations when you’ll need to understand how it works. These include the differences between a forward and backward proxy, how to secure a connection through encryption, and whether a broker should be transparent or distorting.
Table of Contents
Forward vs. Backward Proxy
Typically, a forward proxy and a reverse proxy act differently. However, both are designed to provide security, performance, and reliability benefits. Despite their differences, both serve a similar purpose. Even if you’re starting to work or using these proxies, you need to understand their differences or how proxy works.
A forward proxy is designed to conceal the actual IP address of the server it serves. A reverse proxy, in contrast, works in reverse, intercepting client requests and forwarding them to the desired destination. In addition, a forward proxy can be configured to limit the types of files it accepts or allow only private network connections.
A reverse proxy is designed to protect a web server from attacks. It also can provide benefits such as speed, reliability, and content compression. For example, a reverse proxy can offload a web server by caching static content. In addition, a reverse proxy can limit the size of accessed files.
A forward proxy is a valuable tool for bypassing state or institutional browsing restrictions. A reverse proxy can also serve as a secure communication channel between sites.
A forward proxy is a practical way to hide the actual IP address of a proxy server. A reverse proxy is also helpful in minimizing resources consumed by slow clients. In addition, a reverse proxy is a good tool for complying with data-impacting regulations. It can distribute traffic among several web servers within a local area network.
Transparent vs. Distorting
Using a transparent vs. distorting proxy to surf the internet can be a pain, but they offer several perks. One example is the ability to bypass an IP ban, a feat that would have been more difficult without the help of a proxy. Another is the ability to access remote websites that might be otherwise blocked from your local network. You can also use them to circumvent geo-based content restrictions. Some sites automatically terminate proxy connections, so you’ll need to check their terms of service to find out if you’re in the clear.
A transparent vs. distorting one can help you decide which one to trust. A distorting proxy is not your best bet if you’re a privacy freak. However, it can be a valuable tool for organizations looking to implement one. The most obvious example is a public library or school network administrator. In addition, employers may be interested in using one in other industries, such as law firms, to help protect their client’s privacy. They’re also helpful for companies that want a more hands-on approach to content delivery.
The most important consideration is choosing the right one for you. There are several reputable providers, such as prime and SurfEasy, to name a few. Opt for a transparent vs. distorting service provider if you want the most bang.
Reverse vs. Anonymous
Using a reverse or forward proxy can add flexibility to your website. You can also use a reverse proxy to help prevent data leaks and keep your website safe from malicious attacks.
In addition, you can also use a reverse proxy to enhance performance metrics. For example, a reverse proxy can help monitor suspicious activity and perform protocol switching. This can reduce page load times and protect sensitive assets.
A reverse proxy can be used as a load balancer, distributing incoming traffic among several servers. This ensures that there is always a server available to handle incoming requests. It also maintains the performance of your website.
Reverse proxies can also be used to encrypt data, decrypt data, and cache information. This benefits businesses that store many pictures and videos on their website.
Some internet users want to maintain their anonymity while using the internet. For example, they may want to hide their IP address, or they may want to avoid being targeted by marketers. This is possible with a high anonymity proxy, which can hide a user’s IP address. However, some brokers are unstable and blocked by websites.
Some businesses can also benefit from using a reverse proxy to increase the speed of their website. This is especially useful if there is a large amount of traffic to the website.
Secure Connections Through Encryption
Whether on the internet or a public Wi-Fi network, you must make sure you’re connecting securely. You can do this by using encryption. It protects your data and is also a handy tool. There are several types of encryption, including SSL certificates and Extended Validated credentials.
SSL certificates protect your data by authenticating your server. They also contain a digital signature. This digital signature is used to verify that the certificate issued to your domain name is genuine. This certificate is recognized automatically by browsers and helps protect your connection. There are also multi-domain certificates, which protect up to 100 domains. Alternatively, you can buy a single-domain certificate covering a single subdomain. You can also purchase a wildcard certificate, which protects unlimited subdomains. Ultimately, encryption is an essential tool you should use and is growing in popularity. You can find it easily online, and it will protect your data and help you to make secure connections.
The first step is to make sure you’re using an SSL certificate. You can search for an SSL certificate online or ask your web developer to set up a certificate. Next, you’ll need to agree on encryption and create keys to encrypt the exchanged data.